Hacker Vector Illustration Piratage De La Base De Données Du Serveur Vol De Données | Vecteur Premium

Constructing an Ethical Hacking Knowledge Base for Threat Awareness and Prevention (Hardcover) - Walmart.com

Hackers Controlling Hostile Attack While Working In Hideout Base Stock Photo - Download Image Now - iStock

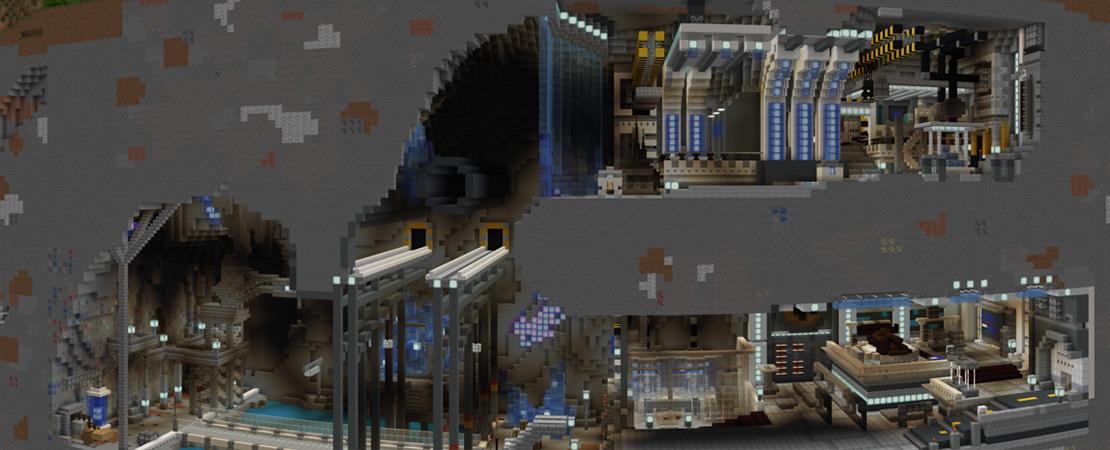
Minecraft Marketplace on Twitter: "One of today's deals is Ultimate Hacker Base by @DodoStudiosNL! Live in this ultimate hacker base and use all the different hacks which are built into the secret

Constructing an Ethical Hacking Knowledge Base for Threat Awareness and Prevention: Dhavale, Sunita Vikrant: 9781522586708: Amazon.com: Books

interface utilisateur pack de 16 lignes d'esprit remplies de couleurs plates de base hacking smoke hack time éléments de conception vectoriels créatifs modifiables 18572653 Art vectoriel chez Vecteezy